The Internet of Things (IoT) is reshaping our world, embedding itself in everything from home appliances to critical infrastructure. With an estimated 75 billion devices expected to be connected by 2025, the digital ecosystem is experiencing an unprecedented expansion. However, with great connectivity comes great responsibility. This surge in IoT devices has inadvertently opened Pandora’s box of vulnerabilities, with many of these devices lacking robust security features. The potential for cyberattacks is not merely a warning sign on the horizon—it’s already at our doorstep. This article delves into the present challenges, emerging solutions, and future predictions in the ever-evolving domain of IoT security.
The Current State of IoT Security
The IoT landscape today is a double-edged sword. On one hand, we’re witnessing an explosion of innovative devices enhancing daily lives and business operations. On the other, a significant portion of these devices remain startlingly insecure. Recent cyberattacks, like the infamous Mirai botnet which hijacked a myriad of insecure IoT devices to launch massive DDoS attacks, serve as grim reminders of the existing vulnerabilities.
The primary threats often stem from weak default passwords, lack of encryption, and outdated firmware. Additionally, with many manufacturers prioritizing speed-to-market over security, a vast number of devices are released with minimal built-in protection.
This rush, combined with users’ general lack of awareness about potential threats, creates a playground for cybercriminals. It’s clear that the current state of IoT security is a patchwork quilt, with too many gaps left exposed.
Challenges of Securing IoT Devices
Securing IoT devices presents unique hurdles, often rooted in the very design and functionality of the devices. Firstly, many IoT devices are designed to be lightweight with limited processing power. This minimalistic approach, while beneficial for efficiency and cost, means that these devices often lack the resources to run complex security protocols. Then there’s the issue of battery life. Implementing robust security measures can be energy-intensive, a luxury that battery-operated IoT devices can’t always afford.
Traditional security solutions, crafted primarily for computers and servers, are not always transferable to the IoT realm. These solutions often require significant computational resources, frequent updates, and user intervention – aspects that are not always feasible for devices like smart thermostats or wearable health monitors. This disparity necessitates a rethinking of our security approach, tailoring solutions specifically for the constraints and needs of IoT devices.
Latest Security Technologies and Trends in the IoT Space
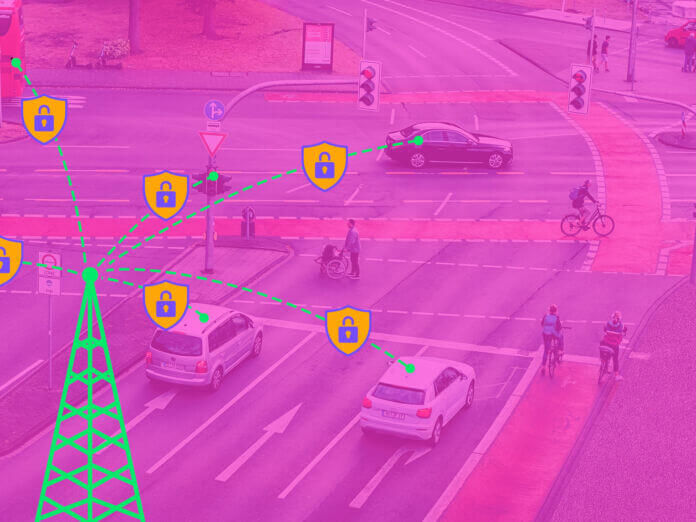
The urgency of IoT security challenges has spurred technological innovations aimed at fortifying these devices. Leading the charge are strategies like end-to-end encryption, which ensures that data transmitted between devices remains confidential and tamper-proof, safeguarding it even if intercepted.
Secure booting, another critical trend, ensures that a device boots up using only the software authorized by the manufacturer, preventing malicious code execution at startup. Additionally, the implementation of hardware-based roots of trust has been pivotal. These are dedicated cryptographic processors that anchor security solutions right from the device’s hardware, ensuring integrity and authenticity throughout the device lifecycle.
Recognizing the stakes, companies are amplifying their investments in IoT security. Global tech giants, as well as nimble startups, are pumping resources into research and development to craft tailored security solutions for the IoT spectrum. Collaboration is the keyword in this arena.
Major tech firms are banding together to formulate standardized security protocols. These alliances aim to ensure that security benchmarks are maintained across the industry, thereby reducing fragmentation and building a unified front against potential threats. The landscape, once fraught with vulnerabilities, is now becoming a hotbed of innovation and collaborative resilience.
Predictions for the Future of IoT Security
The future of IoT security appears to be intrinsically tied to the capabilities of Artificial Intelligence (AI) and Machine Learning (ML). As the complexity of threats evolves, security solutions must be equally agile, and this is where AI and ML promise transformative potential.
Predictive threat analysis, powered by these technologies, will revolutionize how we detect vulnerabilities. Instead of reacting to breaches, we’ll be proactively identifying and neutralizing threats, often before they even manifest.
Beyond threat prediction, the age of manual software updates might soon be behind us. Automated patching, driven by AI’s capability to understand and rectify software vulnerabilities, will ensure that devices are always armed with the latest defenses without any human intervention.
Yet, technology is just one piece of the puzzle. The legislative landscape will play a pivotal role in the evolution of IoT security. Governments worldwide are recognizing the critical nature of the threat and are beginning to draft policies that mandate stringent security standards.
These policies will not only impose penalties on lax security practices but also incentivize innovations in the realm of cybersecurity. The combined might of technology and governance will spearhead a more secure and resilient IoT ecosystem.
Securing Tomorrow: The Imperative of IoT Security Today
The dizzying pace of IoT evolution demands an equally swift security response. As our world becomes more interconnected, the stakes for safeguarding these connections rise exponentially. It’s not just about protecting devices; it’s about safeguarding our digital way of life. The innovations in IoT security are heartening, but we stand at a crossroads.
Companies, both big and small, must prioritize and embed security at the core of their IoT strategies. The call to action is clear: invest, innovate, and collaborate. The future of our digital realm depends on a shared commitment to a secure and trustworthy IoT landscape.




 New Episode
New Episode





 Latest IoT News
Latest IoT News










